Bridging the Maturity Gap: How to Advance Your Threat Intelligence Capabilities
Half of enterprises claim advanced threat intelligence capabilities, yet most security teams still spend their days drowning in alerts they can't contextualize and chasing threats they can't prioritize. This disconnect reveals something important: organizations have confused data accumulation with operational maturity.
Recorded Future's 2025 State of Threat Intelligence report captures this paradox. While 49% of respondents rate their programs as advanced, the challenges they report tell a different story. Integration failures, credibility concerns, and relevance gaps suggest that many teams have built impressive threat intelligence infrastructures without solving the fundamental problem of turning information into timely action.
The Evolution From Reactive to Autonomous Security
Threat intelligence maturity isn't measured by feed subscriptions or dashboard complexity. It's defined by how quickly your organization moves from detecting a threat to neutralizing it, and whether that process requires manual intervention at every step.
Recorded Future's maturity framework maps this progression across four stages. Reactive organizations respond to incidents after they occur, often discovering breaches weeks or months late. Proactive teams hunt for threats using structured processes but still rely heavily on human analysis. Predictive programs identify emerging risks before they materialize into attacks, using pattern recognition and behavioral analytics to spot adversary preparation. Autonomous systems execute most detection and response workflows without human intervention, reserving analyst time for complex investigations and strategic planning.
The gap between proactive and predictive represents the biggest leap most organizations face. It requires shifting from "what happened?" to "what's about to happen?" That transition demands more than better tools. It requires connecting disparate data sources, establishing trust in automated decisions, and aligning security operations with business risk tolerance.
Why Integration Remains the Primary Bottleneck
The 2025 report identifies poor integration as a top-three pain point for 48% of security professionals, with 16% calling it their single biggest obstacle. This isn't surprising when you consider the typical enterprise security stack: SIEM platforms from one vendor, EDR from another, vulnerability scanners from a third, and threat feeds from multiple sources that rarely speak the same language.
Each system generates its own alerts using different severity scales and taxonomies. An indicator flagged as critical in your threat feed might not trigger any response in your SIEM because the two systems don't share context about your environment. Analysts end up as human middleware, manually copying indicators between platforms and adding context that should flow automatically.
This fragmentation creates a second problem: 50% of respondents struggle to verify intelligence credibility. When feeds contradict each other or flag threats that never materialize in your environment, trust erodes. Analysts start ignoring automated alerts and reverting to manual investigation, which defeats the purpose of threat intelligence platforms entirely.
The credibility issue compounds with volume. While 46% report information overload, the real problem isn't quantity but signal-to-noise ratio. Generic threat feeds warn about thousands of malware variants and vulnerability exploits without indicating which ones target your industry, geography, or technology stack. Another 46% say their intelligence lacks environmental relevance, forcing analysts to filter manually rather than focusing on genuine risks.
The Hidden Cost of Maturity Stagnation
Organizations stuck at proactive maturity face consequences that extend beyond security metrics. When threat intelligence requires constant manual intervention, response times stretch from minutes to hours or days. That delay matters critically during active intrusions, where attackers move laterally and exfiltrate data while defenders gather context.
Budget implications accumulate quietly. Teams hire more analysts to handle alert volume rather than investing in automation that would reduce workload. They purchase additional threat feeds hoping more data will improve accuracy, which often worsens the signal-to-noise problem. Security tool sprawl increases as teams add point solutions for specific gaps, creating more integration challenges.
Perhaps most significantly, immature threat intelligence programs struggle to communicate risk to business leadership. When security teams can't connect specific threats to operational impact, executives view security as a cost center rather than a business enabler. Budget requests get denied, strategic initiatives stall, and the maturity gap widens.
Building Connected Intelligence Ecosystems
Advancing maturity requires treating threat intelligence as connective tissue between security tools rather than a standalone function. The goal is creating workflows where intelligence automatically enriches alerts, prioritizes vulnerabilities, and triggers responses without manual handoffs.
Start by consolidating intelligence sources. Most organizations subscribe to multiple threat feeds with significant overlap. Reducing vendors to two or three high-quality sources simplifies integration and improves consistency. Combine external feeds with internal telemetry from your SIEM, EDR, and network monitoring tools to build a unified view of your threat landscape.
Standardization matters more than most teams realize. Adopt common frameworks like MITRE ATT&CK for mapping adversary techniques and STIX/TAXII for sharing indicators. When all your systems use the same taxonomy, correlation becomes possible. Your SIEM can automatically link an indicator from your threat feed to suspicious behavior detected by your EDR, creating high-confidence alerts that warrant immediate investigation.
Automation should focus on enrichment before detection. When an alert fires, automated workflows should immediately gather context: Is this IP address associated with known threat actors? Has it appeared in previous incidents? What assets has it contacted? Does it match any indicators in your threat feeds? Analysts should receive fully contextualized alerts rather than raw events that require 20 minutes of research.
Integration with vulnerability management creates particularly high returns. Threat intelligence platforms can automatically flag which vulnerabilities are being actively exploited in the wild, allowing you to prioritize patching based on real risk rather than theoretical CVSS scores. This connection between threat data and remediation workflows represents a key characteristic of predictive maturity.
AI's Role in Accelerating Maturity
Artificial intelligence addresses several maturity barriers simultaneously, though not in the ways vendors often promise. Large language models excel at summarizing lengthy threat reports and extracting key indicators, reducing the time analysts spend reading. They can normalize data from disparate sources into consistent formats, solving integration challenges that previously required custom code.
Machine learning models identify anomalies in network traffic and user behavior that human analysts would miss, particularly when attackers use slow, low-volume techniques designed to evade threshold-based detection. These models improve continuously as they process more data, adapting to your environment's normal patterns without manual tuning.
The real value emerges when AI handles routine triage and correlation, freeing analysts for complex investigations. A well-configured system can automatically dismiss 70-80% of low-confidence alerts, investigate medium-confidence events by gathering additional context, and escalate only high-confidence threats to human analysts. This filtering transforms alert fatigue into focused investigation.
However, AI introduces new challenges. Models trained on generic datasets may not understand your environment's unique characteristics, generating false positives that erode trust. Adversarial attacks can poison training data or exploit model weaknesses. Organizations need clear processes for validating AI-generated insights and maintaining human oversight of automated decisions, particularly those affecting production systems.
Measuring Progress Beyond Self-Assessment
The gap between perceived and actual maturity suggests that self-assessment alone provides insufficient visibility. Organizations need objective metrics that track operational improvements rather than capability checklists.
Mean time to detect (MTTD) and mean time to respond (MTTR) offer concrete measures of maturity advancement. As intelligence integration improves, both metrics should decrease. Track these separately for different threat categories to identify where your program excels and where gaps remain.
Alert accuracy rates reveal whether your intelligence sources and correlation rules match your environment. Calculate the percentage of escalated alerts that result in genuine incidents versus false positives. Mature programs typically achieve 60-70% accuracy, compared to 10-20% for reactive organizations.
Automation coverage indicates how much of your threat intelligence workflow operates without manual intervention. Measure the percentage of indicators that automatically flow into detection rules, the proportion of alerts that receive automated enrichment, and how many response actions trigger without analyst approval. These metrics should increase steadily as maturity advances.
Business impact metrics connect security improvements to organizational outcomes. Track prevented incidents, reduced dwell time, and avoided costs from early threat detection. These measurements help justify continued investment and demonstrate value to non-technical stakeholders.
The Path to Predictive Operations
Predictive maturity emerges when your intelligence program shifts from responding to threats to anticipating them. This requires visibility into adversary infrastructure before attacks launch, understanding of emerging vulnerabilities before exploits appear, and awareness of geopolitical or industry events that might trigger targeting.
Dark web monitoring provides early warning of credential leaks, planned attacks, and adversary discussions about your organization or sector. When integrated with identity management systems, these insights enable proactive password resets and account monitoring before stolen credentials get used.
Attack surface management continuously maps your external exposure, identifying new assets, misconfigurations, and vulnerabilities as they appear. Combined with threat intelligence about which vulnerabilities attackers currently exploit, this creates a prioritized remediation roadmap based on actual risk rather than theoretical severity.
Adversary tracking follows specific threat groups relevant to your industry and geography, monitoring their tactics, tools, and targets. When a group shifts focus to your sector or begins reconnaissance against similar organizations, you can strengthen defenses against their known techniques before they target you directly.
These capabilities require significant investment in both technology and expertise. Organizations typically reach predictive maturity 3-5 years after beginning their threat intelligence journey, assuming consistent progress and adequate resources.
Autonomous Intelligence: Practical Limits and Realistic Goals
Full autonomy remains aspirational for most enterprises. Legacy systems lack APIs for automated response, compliance requirements mandate human approval for certain actions, and complex investigations still require analyst judgment that AI can't replicate.
Realistic autonomous capabilities focus on high-volume, low-risk decisions. Automatically blocking known-malicious IP addresses, quarantining files matching threat indicators, and disabling compromised accounts represent safe automation targets. These actions occur frequently enough that automation delivers significant time savings while carrying minimal risk of business disruption.
Partial autonomy delivers substantial value even when full automation isn't possible. Automated investigation workflows can gather evidence, interview users via chatbot, and check system logs before escalating to analysts with a complete case file. This approach maintains human oversight while eliminating repetitive tasks.
The 87% of organizations expecting significant improvement within two years face a challenging timeline. Reaching predictive maturity typically requires 18-24 months of focused effort, while autonomous capabilities take longer. Success depends on executive support, adequate budget, and willingness to change established processes—factors that often prove more difficult than technical implementation.
Where to Focus Your Next Investment
Organizations at different maturity stages need different interventions. Reactive teams should prioritize basic integration, connecting threat feeds to their SIEM and establishing automated indicator ingestion. Proactive programs benefit most from enrichment automation and vulnerability prioritization. Predictive organizations should invest in adversary tracking and attack surface management.
Regardless of current state, addressing integration challenges delivers the highest return. A unified intelligence platform that normalizes data from multiple sources and distributes it to all security tools creates the foundation for every subsequent maturity advancement. This investment pays dividends across detection, investigation, and response workflows.
The maturity gap isn't closing because organizations lack ambition or resources. It persists because threat intelligence remains disconnected from the security operations it should enable. Bridging that gap requires treating intelligence as infrastructure rather than information—building the connections, automation, and trust that transform data into decisive action. Use the Recorded Future Threat Intelligence Maturity Assessment to identify your specific gaps, and download the full 2025 State of Threat Intelligence report for detailed benchmarks and implementation strategies.
You Might Also Like

I've Tested Portable Power Stations for Years — Here's What I'd Actually Buy in the Last Hours of the Amazon Big Spring Sale
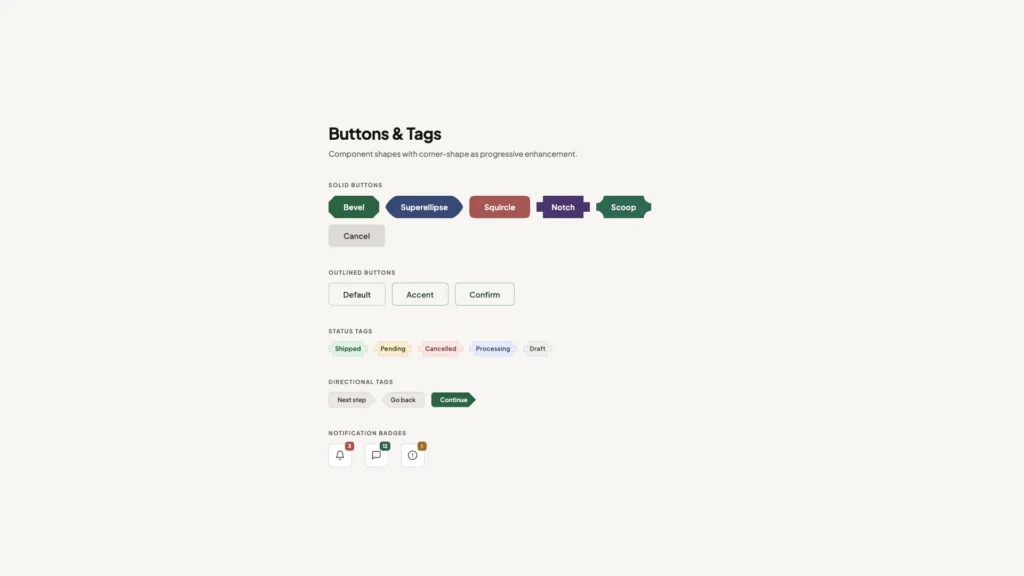
What's !important #8: Light/Dark Favicons, @mixin, object-view-box, and More
